Trust in EAA Issuance and Presentation¶
Overview¶
Electronic Attestations of Attributes (EAA) provide a flexible form of electronic attribute attestations under eIDAS 2.0. They rely on scheme-based trust and existing acceptance structures, offering flexibility, scalability, and cost efficiency for use cases where document-equivalent evidentiary value is not required.
EAA are appropriate when
- Existing acceptance relationships exist between issuer and relying parties
- Document-equivalent evidentiary value is not legally required
- Trust can be established through scheme-based governance
- Cost efficiency and flexibility are important considerations
For guidance on choosing between EAA, QEAA, and PubEAA, see the Trust Overview and Decision Guide.
Trust Model for EAA¶
Scheme-Based Trust¶
For EAA, trust is established through rulebooks or schemes accepted by the relying party. These schemes define:
- Credential semantics and attribute definitions
- Authorized issuers and their requirements
- Trust anchors and validation procedures
- Acceptance conditions
Relying parties explicitly decide which schemes they accept and validate attestations accordingly. This makes EAA:
- Contextual: Trust depends on the specific scheme
- Purpose-bound: Schemes are designed for specific use cases
- Verifier-driven: Relying parties choose which schemes to trust
Issuer Identity Assurance¶
EAA issuers are identified via Access Certificates issued by a Registrar, providing the same cryptographic security level as QEAA and PubEAA issuers.
The key difference from QEAA is not security, but the trust model:
| Aspect | EAA | QEAA |
|---|---|---|
| Issuer identity verification | Access Certificate from Registrar | Access Certificate from Registrar |
| Trust anchor | Scheme governance | EU Trusted List |
| Evidentiary value | Contextual / scheme-dependent | Document-equivalent by law |
| Liability | Contractual / scheme-based | Statutory |
Catalogues of Schemes for Attestation of Attributes¶
National Catalogues¶
Each member state maintains a national catalogue of schemes for the attestation of attributes. For Germany, this includes:
- Scheme definitions and identifiers
- Trust anchors and validation requirements
- List of authorized issuers per scheme
For details on catalogue structure, registration, and governance, see Attribute Catalogues.
Trust-Relevant Content of a Credential Scheme¶
From a trust perspective, a credential scheme defines:
- Issuer requirements: Who may issue attestations under this scheme
- Verification rules: How relying parties validate the attestation
- Trust anchors: What certificates or keys are trusted
For credential design aspects (attribute definitions, revocation mechanisms, signatures), see Design Recommendations
Trust Architecture¶
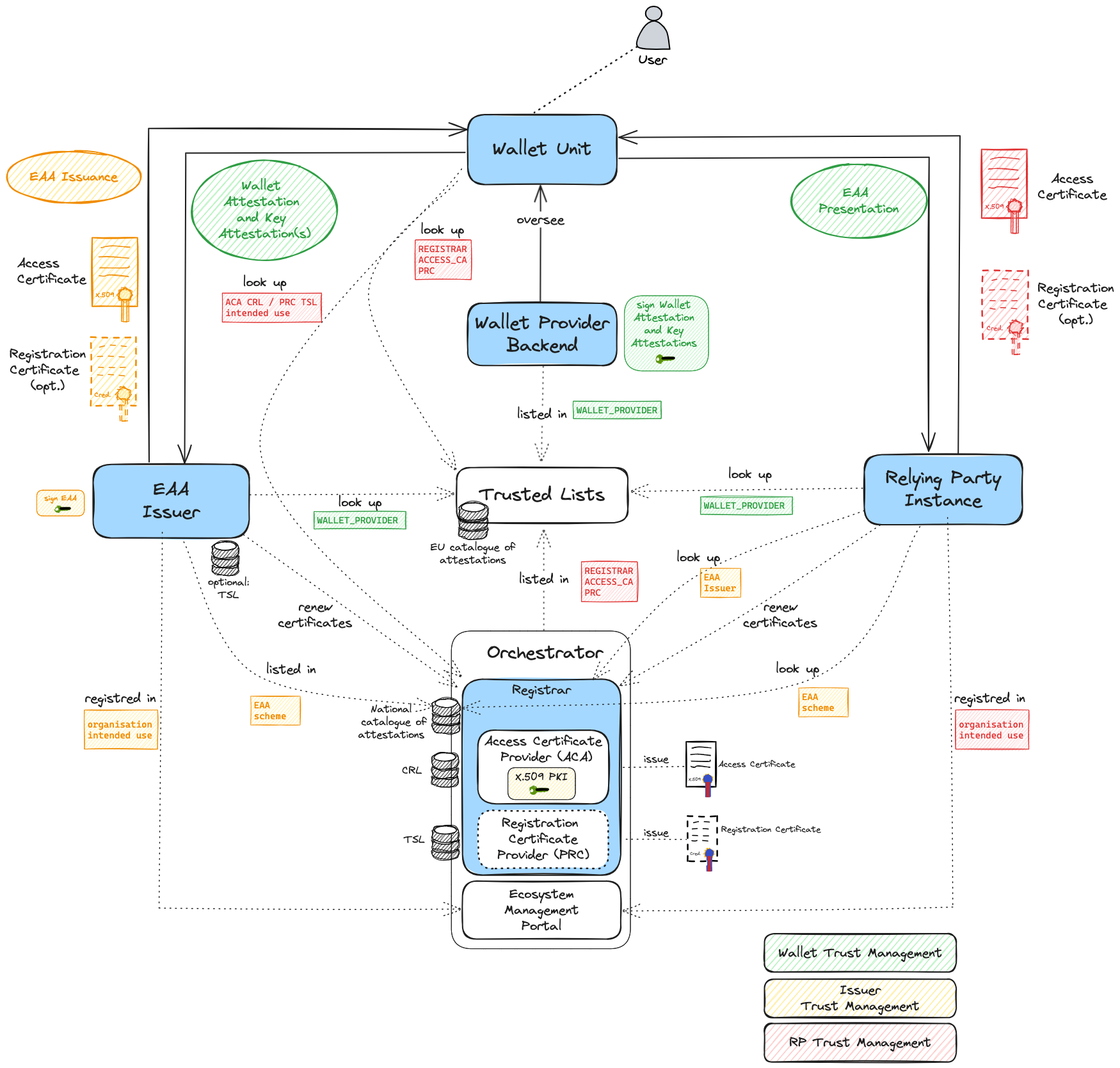
Figure: Trust architecture for issuance and presentation of EAAs
For a description of general trust management between the participants of the ecosystem see Trust Validation Overview.
During EAA Issuance¶
The EAA issuer must:
- Authenticate to the Wallet using its Access Certificate
- Verify the Wallet Unit through Wallet Attestation and Key Attestation(s)
- Obtain attribute data from the authentic source (issuer's own data or authorized source)
- Issue the EAA signed according to the scheme requirements
The Wallet Unit:
- Verifies the issuer's Access Certificate against the national access certificate providers list
- Checks the revocation status of the issuer's certificate
- Optionally verifies scheme membership if required by the scheme
- Stores the EAA after successful validation
During EAA Verification¶
The Relying Party Instance:
- Presents its Access Certificate and Registration Certificate to the Wallet Unit
- Requests specific attributes according to its registered intended use
- Receives the EAA presentation from the Wallet
The Wallet Unit:
- Validates the RP's certificates against national trust lists
- Checks the RP's intended use against the requested attributes
- Obtains user consent for the presentation
- Creates and sends the presentation
The Relying Party then:
- Validates the EAA signature against the scheme's trust anchors
- Checks the EAA's validity via status lists
- Verifies the scheme membership of the issuer (if applicable)
- Applies acceptance rules according to its policies
Legal Effect and Acceptance¶
EAA shall not be denied legal effect or admissibility as evidence in legal proceedings solely on the ground that:
- They are in electronic form, or
- They do not meet the requirements for qualified electronic attestations of attributes
Acceptance of EAA depends on:
- Relying party policies
- Contractual agreements
- Market-related customs, conditions, and practices
- Scheme governance rules
Use Cases for EAA¶
EAA are appropriate for:
- Private sector attestations: Membership cards, loyalty programs, professional certifications (where document equivalence is not required)
- Low to medium risk scenarios: Where official document quality is not legally mandated
- Established trust relationships: Where issuer and relying parties have existing acceptance structures
- Sector-specific schemes: Industry credentials with established governance
- Self-issued attributes: Where the issuer attests their own characteristics
Related Resources¶
- Trust Overview and Decision Guide — For choosing between attestation types
- Trust in QEAA and PubEAA — For qualified attestations
- Trust Validation Overview — For technical validation details
- Wallet-Relying Party Authentication — For RP registration and certificates
- EAA Design Section — For credential design, formats, signatures, and revocation mechanisms
- Design Recommendations — Best practices for well-made EAAs
Legal References¶
Primary Regulation¶
Regulation (EU) No 910/2014 (eIDAS) as amended by Regulation (EU) 2024/1183 (eIDAS 2.0).
Key articles for EAA:
| Article | Topic |
|---|---|
| Article 45d | Electronic attestation of attributes (general framework) |
| Article 45d(3) | Legal effect of electronic attestation of attributes |
ETSI Standards¶
| Standard | Topic |
|---|---|
| ETSI TS 119 472-1 | General requirements for electronic attestations of attributes |
| ETSI TS 119 472-2 | Presentation requirements |
| ETSI TS 119 472-3 | Issuance requirements |
| ETSI TS 119 411-8 | Access Certificates |
| ETSI TS 119 475 | Registration Certificates |